Malware string hash lookup plugin for IDA Pro. This plugin connects to the OALABS HashDB Lookup Service.
The hash algorithm database is open source and new algorithms can be added on GitHub here. Pull requests are mostly automated and as long as our automated tests pass the new algorithm will be usable on HashDB within minutes.
Using HashDB
HashDB can be used to look up strings that have been hashed in malware by right-clicking on the hash constant in the IDA disassembly view and launching the HashDB Lookup client.
Settings
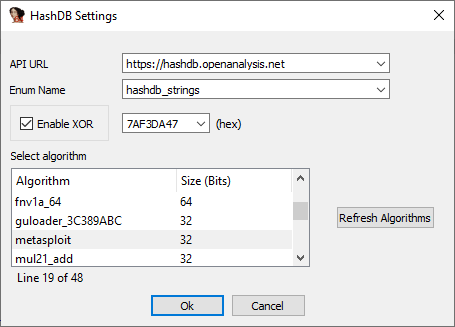
Before the plugin can be used to look up hashes the HashDB settings must be configured. The settings window can be launched from the plugins menu Edit->Plugins->HashDB.
Hash Algorithms
Click Refresh Algorithms to pull a list of supported hash algorithms from the HashDB API, then select the algorithm used in the malware you are analyzing.
Optional XOR
There is also an option to enable XOR with each hash value as this is a common technique used by malware authors to further obfuscate hashes.
API URL
The default API URL for the HashDB Lookup Service is https://hashdb.openanalysis.net/. If you are using your own internal server this URL can be changed to point to your server.
Enum Name
When a new hash is identified by HashDB the hash and its associated string are added to an enum in IDA. This enum can then be used to convert hash constants in IDA to their corresponding enum name. The enum name is configurable from the settings in the event that there is a conflict with an existing enum.
Hash Lookup
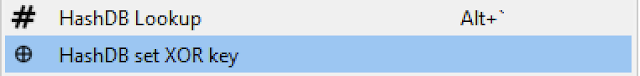
Once the plugin settings have been configured you can right-click on any constant in the IDA disassembly window and look up the constant as a hash. The right-click also provides a quick way to set the XOR value if needed.
Bulk Import
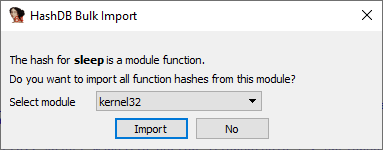
If a hash is part of a module a prompt will ask if you want to import all the hashes from that module. This is a quick way to pull hashes in bulk. For example, if one of the hashes identified is Sleep from the kernel32 module, HashDB can then pull all the hashed exports from kernel32.
Algorithm Search
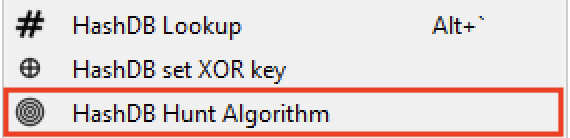
HashDB also includes a basic algorithm search that will attempt to identify the hash algorithm based on a hash value. The search will return all algorithms that contain the hash value, it is up to the analyst to decide which (if any) algorithm is correct. To use this functionality right-click on the hash constant and select HashDB Hunt Algorithm.
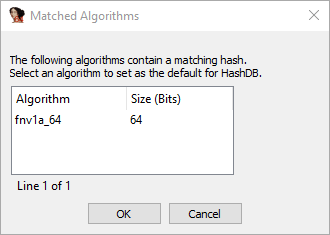
All algorithms that contain this hash will be displayed in a chooser box. The chooser box can be used to directly select the algorithm for HashDB to use. If Cancel is selected no algorithm will be selected.
Instead of resolving API hashes individually (inline in code) some malware developers will create a block of import hashes in memory. These hashes are then all resolved within a single function creating a dynamic import address table which is later referenced in the code. In these scenarios the HashDB Scan IAT function can be used.
Simply select the import hash block, right-click and choose HashDB Scan IAT. HashDB will attempt to resolve each individual integer type (DWORD/QWORD) in the selected range.
Installing HashDB
Before using the plugin you must install the python requests module in your IDA environment. The simplest way to do this is to use pip from a shell outside of IDA.
pip install requests
Once you have the requests module installed simply copy the latest release of hashdb.py into your IDA plugins directory and you are ready to start looking up hashes!
The HashDB plugin has been developed for use with the IDA 7+ and Python 3 it is not backwards compatible.
Continue reading
- Free Pentest Tools For Windows
- Pentest Tools Tcp Port Scanner
- Hack Tool Apk
- Tools Used For Hacking
- Hack Tools Mac
- Pentest Tools Download
- Pentest Tools Subdomain
- How To Make Hacking Tools
- Hacker Tools Github
- Hack Tool Apk No Root
- Hacking Tools For Pc
- Hack App
- Growth Hacker Tools
- Hack Tools Download
- Hacker
- Install Pentest Tools Ubuntu
- Beginner Hacker Tools
- Hacker Tools Windows
- Hack Tools For Ubuntu
- New Hacker Tools
- Hacker Tools Windows
- Hack And Tools
- Hack Tools For Pc
- Hacker Techniques Tools And Incident Handling
- Best Hacking Tools 2020
- Hacking Tools Software
- Hacking Tools For Kali Linux
- New Hack Tools
- Pentest Tools Windows
- Hacking Tools For Windows Free Download
- Tools Used For Hacking
- Hacking Apps
- Hacker Tools
- Hacker Tools For Pc
- Hack Rom Tools
- Hacks And Tools
- Hack Tools 2019
- Hacker Hardware Tools
- Hacker Tools For Ios
- Hacker Tools List
- Hacker Tools For Mac
- Hacking Tools Github
- Pentest Recon Tools
- How To Make Hacking Tools
- Hack Apps
- Game Hacking
- Hack App
- Pentest Tools Open Source
- Hacking Tools
- Tools 4 Hack
- New Hack Tools
- Hacking Tools Windows 10
- Tools 4 Hack
- Hack Tools For Windows
- Pentest Tools Port Scanner
- Pentest Tools Tcp Port Scanner
- Hacking Tools For Pc
- How To Install Pentest Tools In Ubuntu
- How To Install Pentest Tools In Ubuntu
- Hacker Hardware Tools
- Hacking Tools Github
- Pentest Tools Website Vulnerability
- How To Hack
- Beginner Hacker Tools
- Hacking Tools Mac
- Hacks And Tools
- Game Hacking
- Hacker Tools Mac
- Nsa Hacker Tools
- Hacking Tools 2020
- Hacker Tools
- Android Hack Tools Github
- Pentest Automation Tools
- Hacking Tools For Windows
- Hacker Tools Mac
- Pentest Tools Open Source
- What Is Hacking Tools
- Pentest Tools Windows
- Pentest Reporting Tools
- Hack Tools
- Pentest Tools Windows
- Pentest Tools Tcp Port Scanner
- Pentest Tools Website
- Hacking Tools For Pc
- Pentest Tools Bluekeep
- Pentest Tools For Ubuntu
- Hacker Tools Apk Download
- Hacking App
- Hacking Tools For Mac
- Pentest Tools For Ubuntu
- Hacker Tools Online
- Hacking Tools For Windows 7
- Hacking Tools
- Hacking Tools For Mac
- Hack Rom Tools
- Hacking Apps
- Nsa Hack Tools Download
- Hack Website Online Tool
- Underground Hacker Sites
- Ethical Hacker Tools
- Pentest Tools Find Subdomains
- Hacking Tools Software
- Hacking Tools For Games
- Hacking Tools Download
- Termux Hacking Tools 2019
- Hack Tools For Games
- Hacker Tools Github
- Tools For Hacker
- Wifi Hacker Tools For Windows
- Game Hacking
- Hacking Tools Windows
- Pentest Tools Nmap
- Hack Tool Apk No Root
- Hacker Tools For Pc
- Nsa Hack Tools
- Free Pentest Tools For Windows
- Hacking Tools Software
- How To Hack
- Hacking Tools Windows
- Hacking Tools Hardware
- Hacking Tools Hardware
- New Hack Tools
- Pentest Tools Linux
- Hacker Hardware Tools
- Best Pentesting Tools 2018
- Pentest Tools Download
- Hacker Tools For Pc
- Hacking Tools Online
- How To Hack
- Hack Tools
- Hacking Tools For Kali Linux
- Hacker Hardware Tools
- Hacking Tools For Windows
- Pentest Tools Url Fuzzer
- Nsa Hack Tools
- Hacking Tools Usb
- Hacking Tools Usb
- Hacking Tools Usb
- Growth Hacker Tools
- Nsa Hack Tools Download
- Nsa Hack Tools Download
- Beginner Hacker Tools
- Hacker Search Tools
- Hacking Tools For Windows Free Download
- Pentest Tools List
- Hacks And Tools
- Hacker
- Hacking Tools Software
- Hacker Tools Free
- Ethical Hacker Tools
- Pentest Tools Android
- Hacking Tools Github
- Hacking Tools Github
- Pentest Tools Free
- Pentest Tools Linux
- Hacking Tools For Games
- Pentest Tools Android
- Hack Apps
- Hacker Tools For Pc
- Free Pentest Tools For Windows
- Hacking Tools And Software
- Hackers Toolbox
- Hack Tools For Mac
- Pentest Automation Tools
- Pentest Tools Download
- Pentest Tools For Android
- Hacker Tools Apk
- Pentest Recon Tools
- Hacker Tool Kit
- Hack Tools 2019
- Pentest Reporting Tools
- Pentest Tools Windows

No comments:
Post a Comment